In the rapidly maturing digital economy, asset custody has transitioned from a traditional financial concept into a critical pillar of the blockchain ecosystem. As institutional capital enters the market and on-chain applications grow in complexity, the “single private key” management model is no longer sufficient for enterprise-grade security requirements.
In this landscape, Enterprise-Level MPC (Multi-Party Computation) Wallets 及 MPC Self-Custody have emerged as the gold standards for high-security asset management. By leveraging distributed signing mechanisms and multi-layered risk management, these solutions move beyond traditional private key storage to build a robust, scalable, and auditable security framework for digital assets.
Establishing Formalized Signing Protocols for Enterprise Assets
On a blockchain, asset ownership is not tied to an account identity but to signing authority. Whoever generates a valid signature controls the assets. Consequently, the essence of asset custody is not merely data storage, but the sophisticated management of signing permissions.
Traditional single-private-key management presents several systemic vulnerabilities:
- Absolute Risk: If the key is compromised, assets are lost instantly.
- Single Point of Failure: No redundancy in case of loss or theft.
- Insider Threats: A single individual can execute unauthorized transactions.
- Governance Gaps: Lack of hierarchical approvals and compliance audit trails.
For institutional players, these risks are magnified by the scale of capital involved. Enterprise-grade custody must therefore shift toward a distributed key management architecture.
Defining the Enterprise-Level MPC Wallet
An Enterprise-Level MPC Wallet is a professional-grade solution built on Multi-Party Computation. Unlike traditional wallets, MPC allows multiple parties to perform joint computations (such as signing a transaction) without any party ever revealing their private data to others.
The Technical Foundation
In an MPC-based architecture:
- The private key is never created in its entirety; instead, it exists as multiple key shards.
- Each shard is stored on geographically or logically isolated nodes.
- Signatures are generated collaboratively via a distributed protocol.
- The full private key is never reconstructed, eliminating the primary attack vector.
The Shift Toward MPC Self-Custody
MPC Self-Custody empowers organizations to maintain full control over their assets without relying on a third-party custodian, all while utilizing the security benefits of MPC.
The core philosophy is centered on autonomy: the enterprise controls all key shards, ensuring that no single shard—and no single person—can compromise the treasury. Compared to traditional self-custody (which often involves a single hardware wallet or paper backup), MPC self-custody offers a superior security grade by decentralizing control and enabling multi-role collaboration.
Strategic Advantages of Institutional MPC Wallets
Eliminating Single Points of Failure
In an MPC environment, compromising a single node or device yields nothing for an attacker. A signature requires a threshold of participants, ensuring that the “private key” is never a stationary target.
Granular Governance and Control
Enterprises can distribute key shards across different departments—such as Finance, Risk Management, and Executive Leadership. This facilitates:
- Customizable Approval Workflows: Requiring “M-of-N” participants to authorize a move.
- Role-Based Access Control (RBAC): Assigning different weights or permissions to different stakeholders.
- Transaction Limits: Setting thresholds for automated vs. manual approval.
High-Concurrency Operations
Unlike traditional cold storage, which is secure but slow, Enterprise-Level MPC Wallets are designed for the speed of modern finance, supporting high-frequency signing and automated trading environments without sacrificing security.
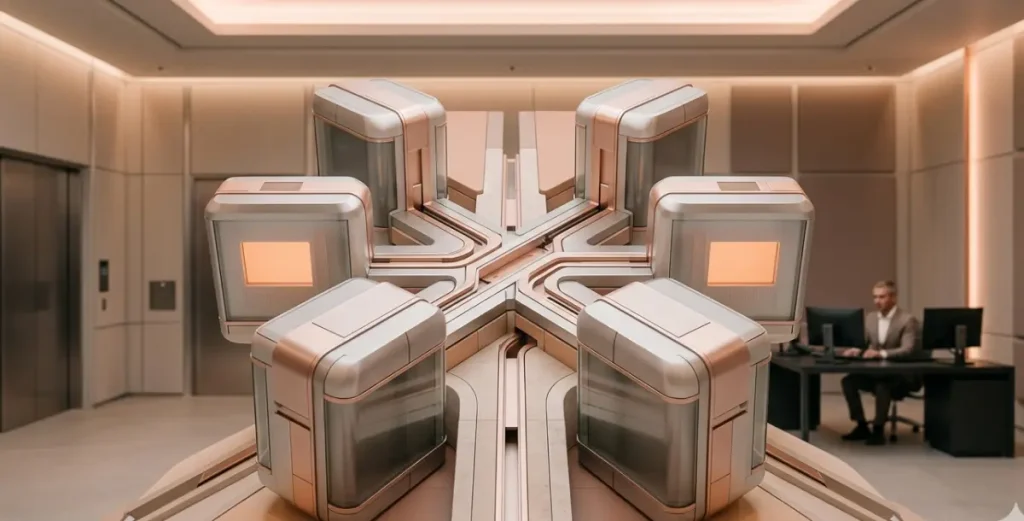
A Tiered Architecture for Digital Asset Management
Professional custody typically employs a three-tier structure to balance liquidity and security:
- Cold Storage Layer: Reserved for long-term holdings with the highest signing thresholds.
- Operational Layer: Handles mid-sized capital, utilizing multi-party approval workflows for daily operations.
- Liquidity/Hot Layer: Used for automated trading and high-velocity movements, protected by real-time risk engines.
Comparing MPC Self-Custody to Traditional Models
| Feature | Traditional Third-Party Custody | MPC Self-Custody |
| Key Ownership | Held by the custodian | Held by the enterprise (shards) |
| Trust Model | Trust in the provider’s integrity | Trust in cryptography and internal policy |
| Counterparty Risk | Risk of provider insolvency or misappropriation | No third-party risk; assets are always on-balance-sheet |
| Flexibility | Subject to provider’s withdrawal windows | Real-time, 24/7 control |
Threat Modeling and Risk Mitigation
- External Attacks: An adversary must breach multiple independent environments simultaneously to generate a signature.
- Internal Collusion: No single employee can move funds; the system mandates collusion-resistant workflows.
- Device Loss: Losing a single device does not result in asset loss, as the shard can be rotated or recovered via the remaining participants.
- Disaster Recovery: Distributed shards ensure that even if one office or region goes offline, the enterprise maintains access to its funds.
Future Horizons in Distributed Custody
As the industry matures, we expect MPC self-custody to integrate more deeply with:
- Dynamic Thresholds: Automatically adjusting signing requirements based on transaction risk scores.
- On-Chain Governance: Linking custody permissions directly to DAO or corporate governance protocols.
- Decentralized Identity (DID): Using verifiable credentials to verify the identity of the signers within the MPC protocol.
The Era of Distributed Trust
Digital asset custody has evolved from simple “key storage” into a complex system of cryptographic engineering. Enterprise-Level MPC Wallets have removed the inherent fragility of the single private key, while MPC Self-Custody provides the autonomy that institutional players require to manage their balance sheets effectively.
In the world of blockchain, signing authority is the ultimate form of control. By implementing a distributed signing architecture, enterprises can achieve a rare harmony: the highest level of security paired with institutional-grade operational efficiency. True maturity in digital asset management is no longer about trusting a single entity—it is about trusting a framework built on mathematics and institutional discipline.