As the digital asset ecosystem matures, security remains the primary concern for both retail users and institutional participants. In traditional cryptocurrency environments, asset security is heavily reliant on a single private key. This creates an inherent vulnerability, exposing the treasury to risks ranging from sophisticated cyberattacks and physical loss to internal unauthorized access. As a result, Multi-Party Computation (MPC) 及 Non-Custodial MPC Wallets have emerged as the industry’s strategic response to these systemic risks.
By fragmenting the private key and distributing the signing process across multiple independent nodes, MPC significantly hardens the security of asset management. When integrated with a non-custodial framework, it empowers users to maintain absolute sovereignty over their assets without relying on a centralized intermediary. This synergy represents a shift toward more resilient, decentralized, and transparent infrastructure.
Understanding Multi-Party Computation (MPC) Technology
Multi-Party Computation (MPC) is a cryptographic subfield that enables multiple parties to jointly compute an output over their private inputs without revealing those inputs to one another. In the context of digital assets, MPC is primarily utilized for Distributed Key Management and transaction signing.
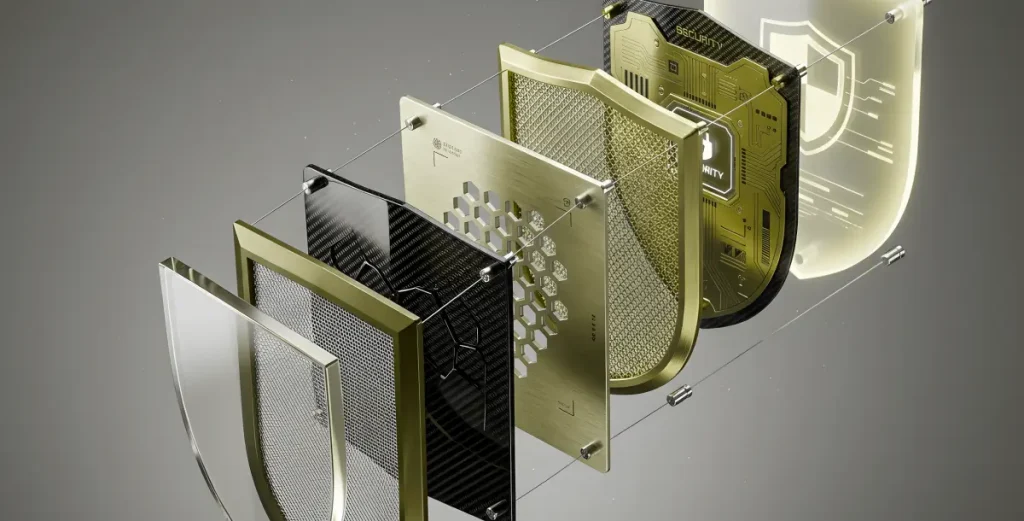
Legacy wallet architectures rely on a single, static private key to authorize transactions; if this key is compromised, the associated assets are lost. MPC eliminates this Single Point of Failure (SPOF) by breaking the private key into multiple “Key Shards.” Each shard is stored on a separate node, and valid signatures are generated through secure computation without the full private key ever being reconstructed on any single device.
Technical Foundations
A robust MPC framework is built upon four critical pillars:
- Key Sharding: The singular private key is mathematically divided into multiple shares, ensuring no single entity holds the full credential.
- Distributed Signing: Transactions are authorized through the collective participation of independent nodes holding these shares.
- Privacy-Preserving Computation: The protocol ensures that no individual node can infer the value of other key shares during the signing process.
- Fault Tolerance: The system remains operational and accessible even if a subset of nodes goes offline, ensuring high availability.
Defining the Non-Custodial MPC Framework
A non-custodial architecture ensures that the user retains exclusive control over their cryptographic keys and underlying assets. This eliminates counterparty risk, as no third-party institution has the unilateral power to freeze, seize, or mismanage the user’s funds.
Integrating MPC with Non-Custody
The Non-Custodial MPC Wallet represents an evolution in digital ownership by providing:
- Decentralized Governance: Users maintain control over their key shards, removing reliance on centralized custodians.
- Multi-Layered Defense: Asset security is maintained even if an individual node or device is compromised.
- Operational Flexibility: Supports complex threshold signing policies, multi-device management, and granular permissioning.
- Abstracted User Experience: Users benefit from high-level security without the operational friction of managing a 24-word seed phrase.
Strategic Advantages of Non-Custodial MPC
Mitigation of Single Points of Failure (SPOF)
By moving away from singular private keys, MPC wallets force an attacker to compromise multiple, heterogeneous environments simultaneously to gain access to funds. This fundamentally shifts the cost-to-attack ratio in the user’s favor.
Institutional-Grade Security & Compliance
For enterprise users, non-custodial MPC wallets integrate seamlessly with corporate governance structures to provide:
- Multi-User Approval Workflows: Ensuring no single individual can authorize a high-value transfer.
- Immutable Audit Trails: Facilitating transparent risk management and regulatory reporting.
- Distributed Operational Oversight: Real-time monitoring of signing activity across the organization.
Alignment with Decentralized Principles
MPC allows users to manage assets with institutional-level security while adhering to the core blockchain tenet of self-sovereignty, enhancing both privacy and asset control.
Technical Implementation Requirements
To deploy a professional-grade Non-Custodial MPC solution, several technical benchmarks must be met:
- Distributed Key Management (DKG): Ensuring shards are generated and stored in isolated environments (e.g., mobile, cloud, and HSM).
- Zero-Knowledge Signature Generation: Utilizing advanced cryptographic proofs to ensure signatures are valid without exposing shard data.
- Role-Based Access Control (RBAC): Setting transaction thresholds and administrative policies to govern asset movement.
- High Availability & Disaster Recovery: Ensuring the system remains resilient against localized node failures or connectivity issues.
Primary Use Cases
- Digital Asset Exchanges: Hardening exchange infrastructure to protect user liquidity against external breaches.
- Institutional Asset Management: Supporting sophisticated “M-of-N” signing strategies for hedge funds and family offices.
- Web3 & DeFi Interaction: Securely managing smart contract interactions and treasury funds for DAOs and projects.
- Cross-Chain Interoperability: Utilizing distributed signing to facilitate secure transactions across multiple disparate blockchain protocols.
Strategic Evolution & Roadmap
The future of MPC-based security is trending toward abstracted complexity 及 active defense:
- Optimized Signing Performance: Next-generation algorithms designed to reduce computational latency.
- Simplified Onboarding: Leveraging social recovery and biometrics to remove the technical barriers of entry.
- AI-Enhanced Risk Engines: Proactive monitoring systems that can autonomously block signatures for high-risk or anomalous transactions.
- Native Cross-Chain Support: Unified key management frameworks that handle multi-chain assets through a single distributed signature.
The convergence of Multi-Party Computation 及 Non-Custodial architecture provides a definitive solution to the security-convenience trade-off. By leveraging distributed key management and decentralized signing, this framework allows both retail and institutional participants to secure their assets without sacrificing autonomy. As the digital economy scales, MPC wallets are positioned to become the foundational security layer, safeguarding the future of global digital sovereignty.